Summary
This is part 3 of a series looking at email security.
The schedule and content of the other parts might change as they are released over the next few months, but each article will contain an up-to-date table of contents.
- Part 1 - Overview and general advice
- Introduction
- Dos and don'ts
- Part 2 - S/MIME certificates: what they are, how they work and how to obtain one free of charge
- What is S/MIME?
- Public-Key Cryptography
- How does digital signing work?
- What about encrypting the message?
- Obtaining a free S/MIME certificate
- Part 3 - Signing and encrypting emails with S/MIME
- Using S/MIME on Windows with Outlook and Thunderbird
- Using S/MIME on the Apple Mac
- Using S/MIME in Outlook Web App (in Office 365)
- Using S/MIME on Android, iOS and Windows Phone
- Part 4 - PGP keys: what they are and how to obtain one free of charge
- What is PGP?
- Obtaining a PGP key
- Part 5 - Signing and encrypting email with PGP
- Using PGP on Windows with Outlook, Thunderbird, etc
- Using PGP in Outlook Web App (in Office 365)
- Using PGP on Android, iOS, Windows Phone
- Part 6 - DKIM and SPF
- What are they and how do they work? Something to do with DNS records?
- Part 7 - Sending signed emails programmatically
- Sample code to sign and send emails. Probably written in C# to be delivered via ASP.NET Web API 2.
- Part 8 - Conclusions and further thoughts
Introduction
In Part 2 we learnt what S/MIME is, how it works and discovered how we can obtain an S/MIME certificate for free. This time we're going to learn how to install and use the certificate we obtained. So, if you haven't already done so, follow these instructions and get your free S/MIME certificate now, remembering that you need initially to install the certificate on the same machine from which the original key request was made, due to the fact that the private key only exists on that machine in the first instance. You can always export your certificate and key for installation elsewhere and that's what we'll be looking at first.
Exporting the certificate
On Windows you can press Win + R and type certmgr.msc to bring up the certificate manager and then choose Certificates - Current User → Personal → Certificates to find the certificate with your email address.
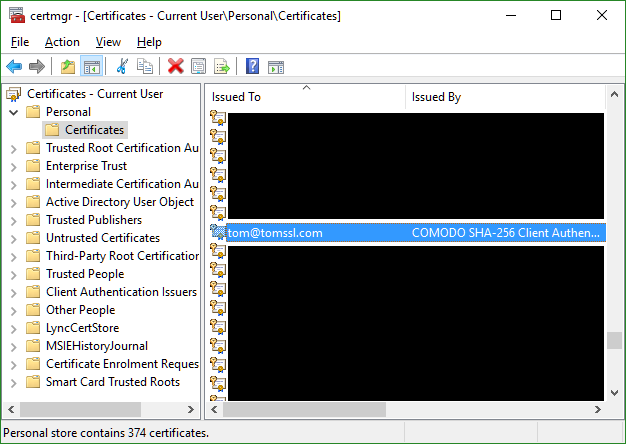
You can view the certificate by double-clicking on it, or you can right-click on it and choose All Tasks → Export... to start the Certificate Export Wizard.
If you're running Chrome then perhaps the easiest way to export the certificate is to go to the settings menu (Alt + E) immediately after you've collected it and choose Settings → + Show advanced settings → HTTPS/SSL → Manage certificates... and find your certificate in the Personal tab.
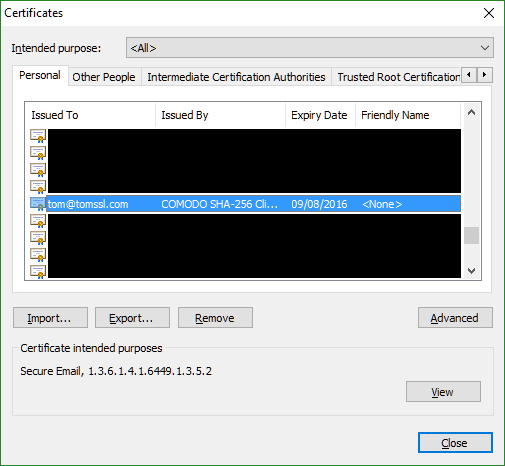
Again, you can double-click to view the certificate or click the Export... button to start the Certificate Export Wizard.
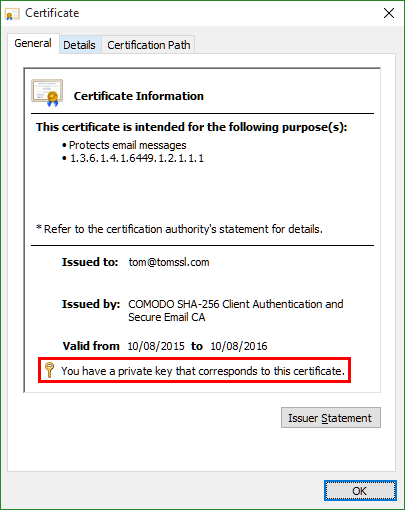
Viewing the certificate
If you elect to view the certificate, notice that you have the corresponding private key installed on your computer. This is important since the way the signing of emails using S/MIME works relies on your being in sole control of your private key and using it to encrypt message digests which may then be decrypted using your public key. As the name implies, the public key is generally available and is in fact contained in the certificate that accompanies the email message. This is all explained in considerable detail in Part 2, but the salient point is that, in order to sign your emails, you need the private key.
The Certificate Export Wizard
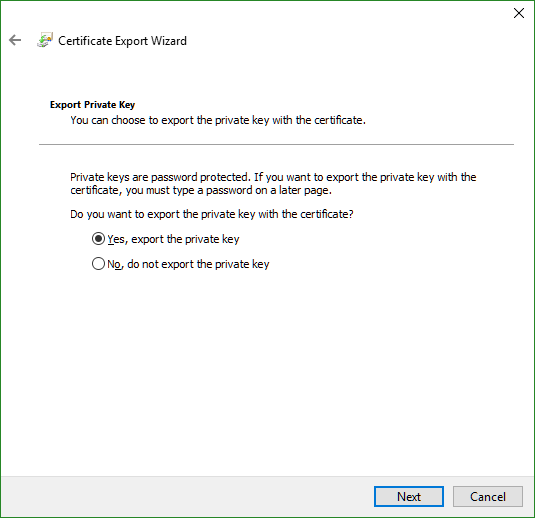
The first question the Certificate Export Wizard asks you is whether or not you want to export the private key and by now you know that the answer is yes.
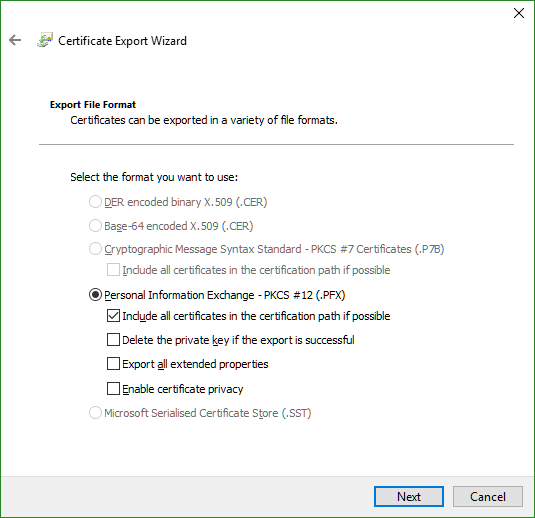
Next you need to choose the file format. Actually, you don't really, as it will already have been set to Personal Information Exchange - PKCS #12 (.pfx file extension) due to the fact that you are exporting the private key. It's worth checking the first option - Include all certificates in the certification path if possible.
Now you need to choose a password. I advise using a password manager to create and store your passwords. I'll be writing more about this in a future article.
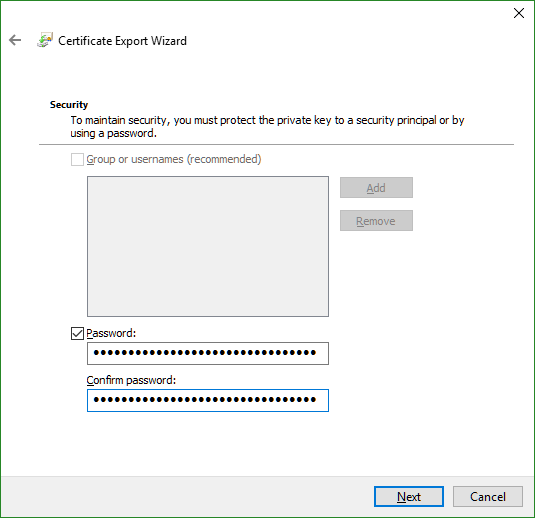
Important: Anybody who has your
.pfxfile and password can send email that is signed as having come from you. Worse than that, if they get hold of encrypted email that has been sent to you, they can decrypt it. Choose a strong password and keep it secure.
The final two steps involve choosing a filename and being shown a summary of the settings you've chosen, after which clicking on the Finish button should result in this:
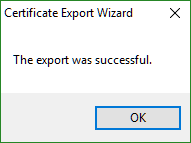
Now you have your S/MIME certificate stored in a password-protected file ready to be imported and used wherever you like.
It should be noted that it may not be necessary to export the certificate to use it on the same computer, depending on which mail application you want to use it with. If you're using Outlook, for example, then you won't need to export it. If you want to use it on a different machine (e.g. a mobile phone) then of course you will have to export it.
Using S/MIME on Windows with Outlook or Thunderbird
Having given us a free certificate, at first glance it appears that Comodo also tell us how to install it but, unfortunately, these instructions seem to be somewhat out of date, to say the least. Don't bother clicking on that link unless you're running an ancient and unsupported version of Outlook.
Outlook 2010/2013
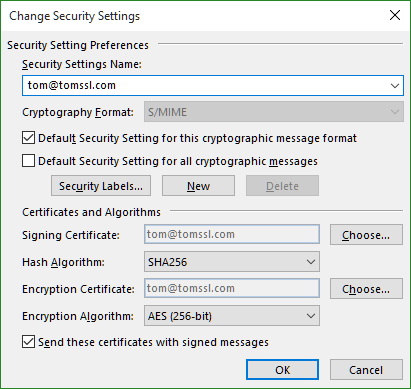
If you're running Outlook 2010 or 2013 then go to File → Options → Trust Center → Trust Center Settings... → E-mail Security → Settings...
Now click on the Choose... button and select the certificate which corresponds to your email address. When you've finished your settings should look something like this:
To make life easier for myself, the next thing I did was to add the Sign and Encrypt functions to the Quick Access Toolbar (which usually appears at the top of the window).
Click New Email and then click the small drop-down on the right of the Quick Access Toolbar and choose More Commands... → Quick Access Toolbar or, alternatively (and more easily), simply press Alt, F, T, Q one after the other.
In the window that appears, select Choose commands from: All Commands and then select Digitally Sign Message and Encrypt and Add » them to the right-hand side. You might also want to experiment with the position of the toolbar relative to the ribbon.
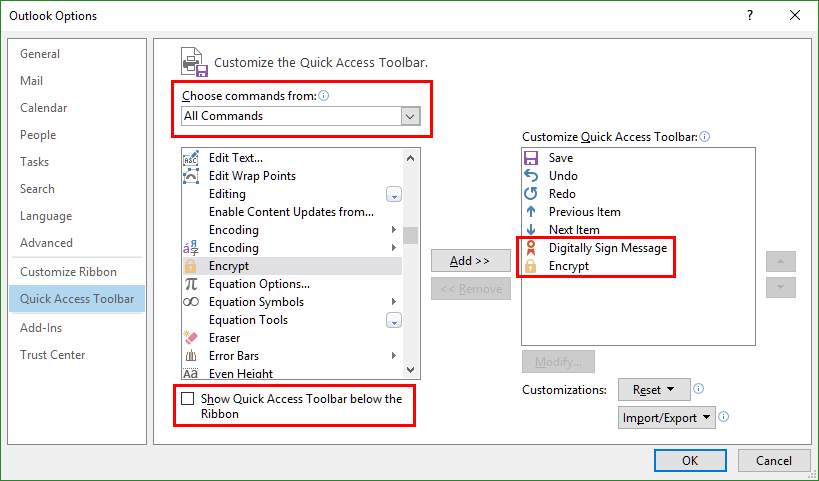
If the Digitally Sign Message and Encrypt menu options do not appear, you are probably customising the main Quick Access Toolbar and not the one specific to composing an email. Make sure you choose New Email and then follow the steps above.
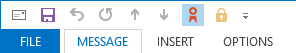
Now when you are writing a new message, you can easily choose whether to sign or encrypt the message by clicking on the buttons at the top of the window or by pressing Alt and then choosing the number which corresponds to the menu item. In this example I am signing the message (Alt, 6), but not encrypting it (Alt, 7).
Thunderbird
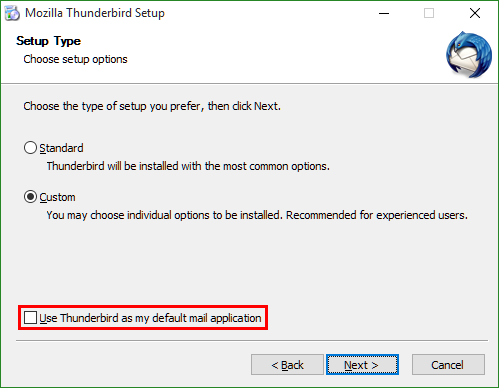
Thunderbird is a free email client from Mozilla. First download it from https://www.mozilla.org/en-GB/thunderbird/
I did that just now and got version 38.5.1.
Pay attention when you're installing it, in case you don't want to make it your default mail application.
Once you've installed Thunderbird, you need to set up your email account. If you're using Office 365 then you need to configure it as an IMAP account. To get your IMAP settings for Office365 from the Outlook Web App, click on the cog and choose Options → Mail → Accounts → POP and IMAP or, alternatively, just click on this link: https://outlook.office365.com/owa/#path=/options/popandimap.
Once your account is up and running go to Settings → Security → View Certificates and you will see that Thunderbird uses a separate certificate store (i.e. there are no certificates).
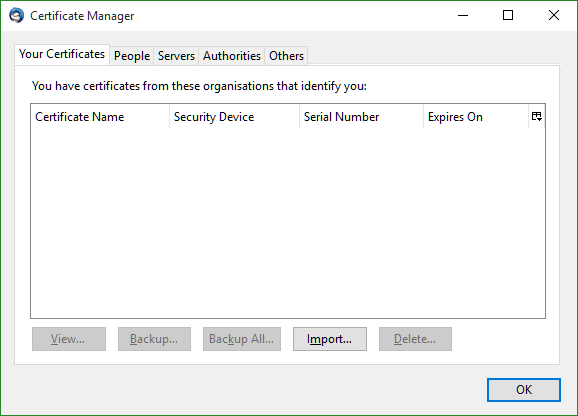
Click Import... and choose the .pfx you exported earlier. Once this is done you will see something like this:
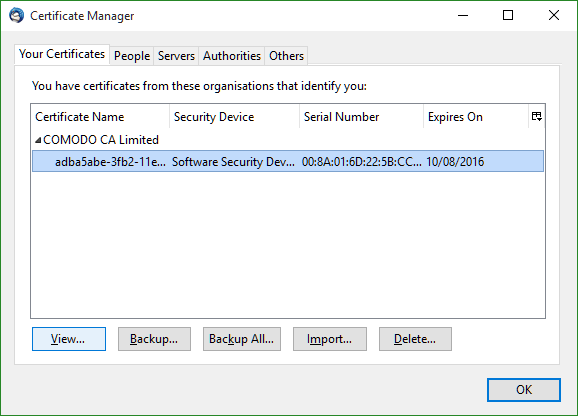
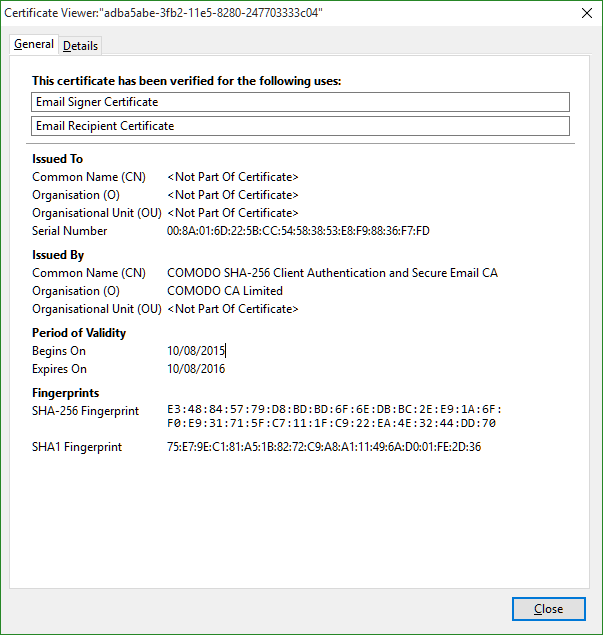
Choose View... to see what may be a disconcertingly vague, but accurate, summary of your certificate.
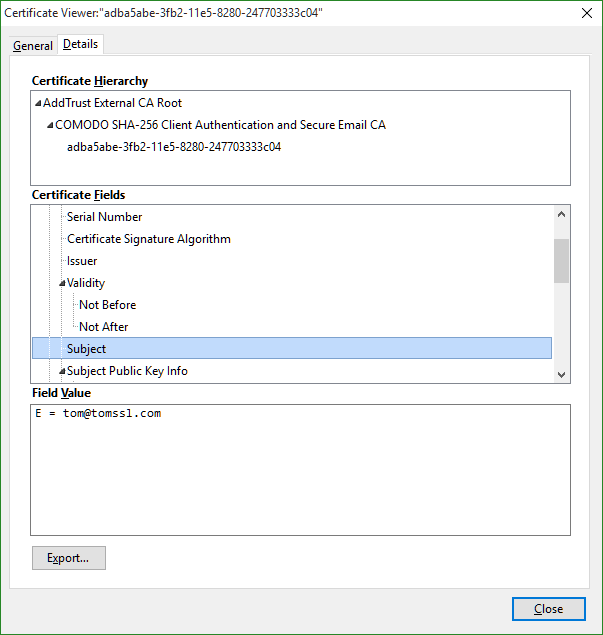
To see anything useful you'll need to click on the Details tab and choose Certificate Fields → Subject to see your email address.
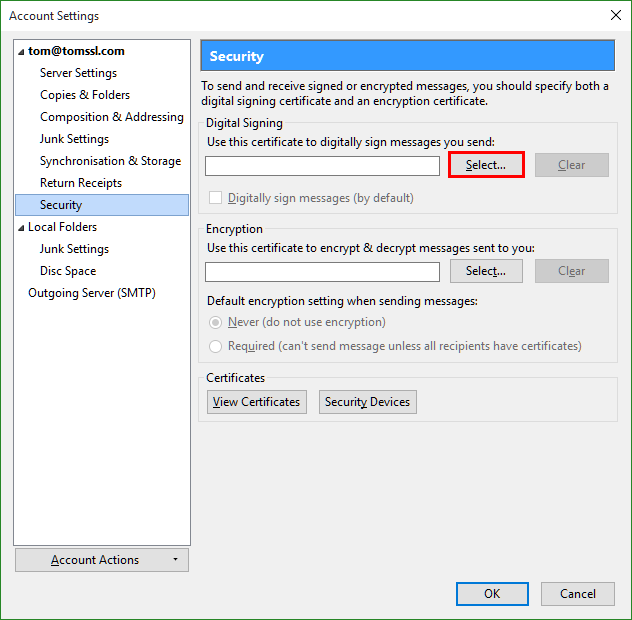
Once you close the certificatemanager you should still be in the Settings → Security window where you should now choose Select... as shown below.
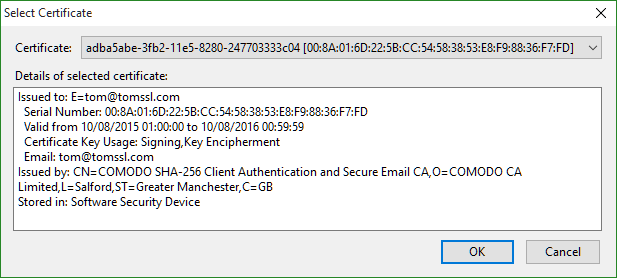
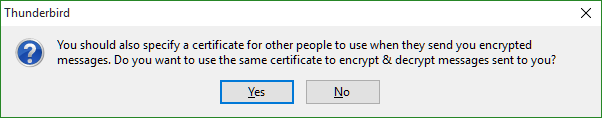
Select your certificate and say Yes when it asks you if you want to use the same one for encryption.
Once this is done Settings → Security will contain a bit more information.
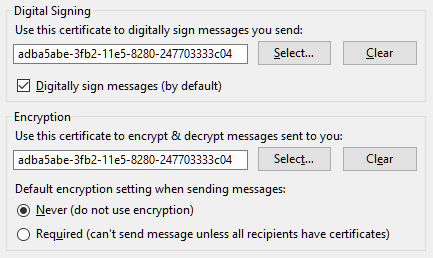
Click Ok and you're ready to go.
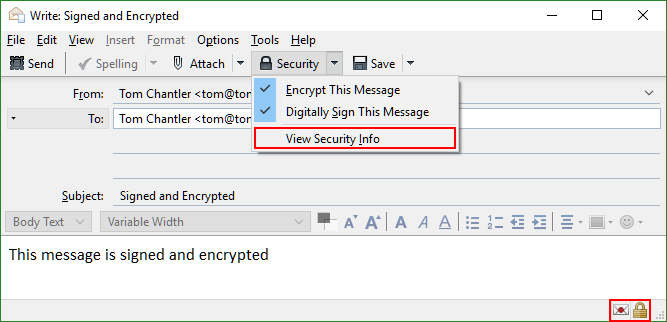
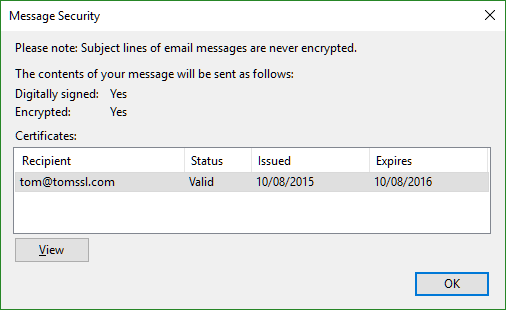
When you write an email, it's very easy to use your certificate. You can choose to sign and/or encrypt your message in the Security menu and clicking on Security → View Security Info or on the icons at the bottom right (indicated below) will bring up a message security dialog showing the validity or otherwise of the recipient (e.g. do you have a copy of their public key if you are trying to send them an encrypted email). This is really good.
I hadn't used Thunderbird before and I was very impressed by it.
Signing and encrypting messages in the browser with Outlook Web App for Office 365
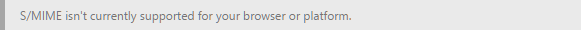
Annoyingly, the S/MIME control is an ActiveX application, which means that it neither works in Chrome, nor in Edge. In fact it only works in Internet Explorer.
If you try to read an encrypted message in an unsupported browser (i.e. anything except IE) then you get this:
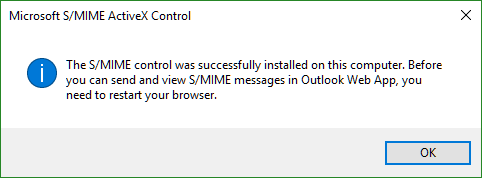
Whereas in IE you get this:

Closely followed by this:
When composing a new message, if you click on the ellipsis at the top of the compose window and choose Show message options... then apparently you can choose to sign and/or encrypt the message using your S/MIME certificate, although I didn't get this to work and gave up trying fairly quickly.
This lack of support is quite frustrating and I have no idea if this functionality will be coming to the Edge browser. You can read more about it here.
Using S/MIME on the Apple Mac
A few months ago I was talking about this article with a Mac-owning friend of mine and he kindly offered to provide me with instructions and screenshots for installing the certificate on a Mac, for inclusion in this article.
After registering for a free certificate from Comodo as described in Part 2, he clicked on the link in the email and used Safari to download a file called CollectCCC.p7s to the Downloads folder on the Mac.

Double-clicking on this file automatically installed it into the Keychain on the Mac. This was verified by opening Keychain Access through Spotlight and then checking that the certificate had been installed under My Certificates. The category Certificates shows all certificates which have already been received, including all signatures received via email.
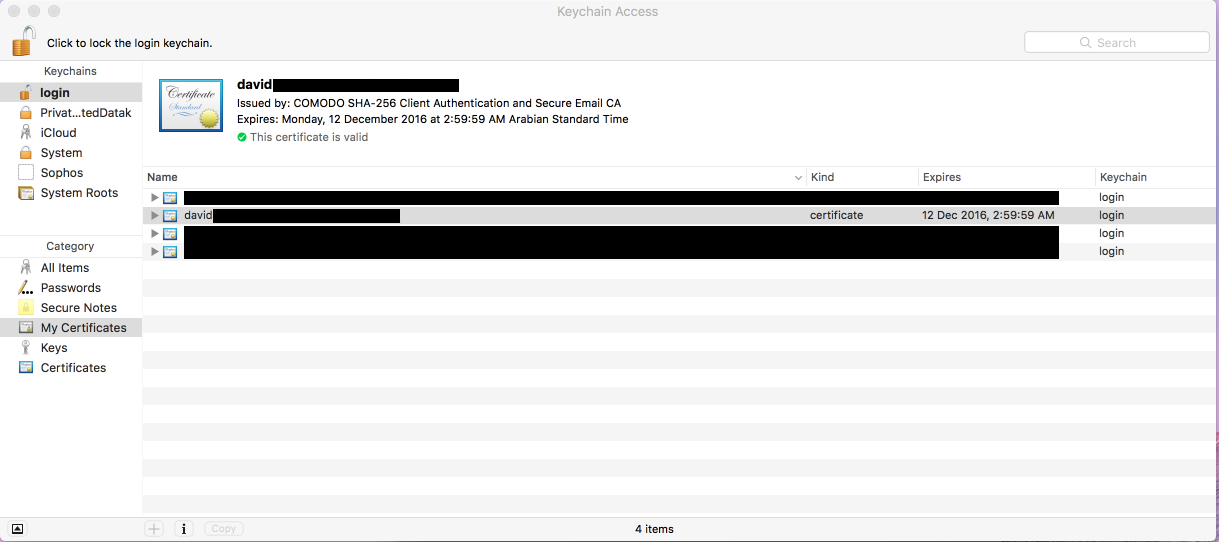
Having done this, it's possible to confirm that your email address now has a valid digital signature by opening Contacts and checking that your own details have a checkmark next to the signed email address.
To get the Mail app to use your new certificate, you have to quit Mail and restart.
Many thanks to my friend David for helping with this. He was very patient as we exchanged a number of test emails.
Using S/MIME on Android, iOS, Windows Phone
Android
Coming very soon (I don't currently have an Android device).
iOS
After I'd exported my certificate and given it a very strong password, I emailed it to myself and collected the email on my iPhone. Then I clicked on the .pfx attachment and installed it.
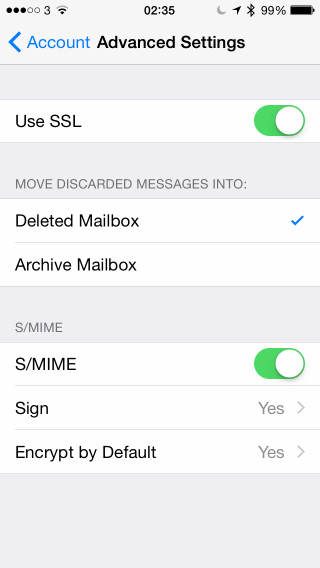
Then I went to Settings → Mail, Contacts and Calendars and selected my mail account. Then I chose Account → Advanced Settings → S/MIME and selected Yes to each of the options Sign and Encrypt by Default, selecting my just-installed certificate for each.
When you receive a signed email, it looks like this:

And if it's signed and encrypted, it looks like this:

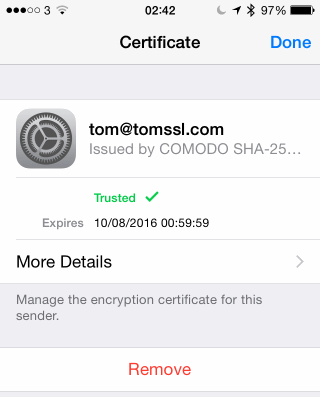
You can then click on the sender details and view and install the certificate.
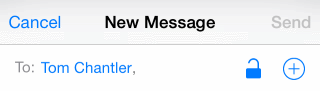
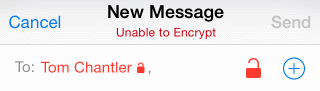
Now when you send an email message, if it is just going to be signed then there will be an open padlock next to the recipient's name. You can tap on the padlock to toggle encryption on and off (as long as you have a copy of their public key).
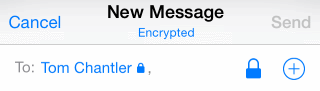
And if you can't encrypt the message, this happens. It's pretty self-explanatory.
Note: Microsoft Outlook for iOS doesn't support S/MIME certificates. You have to use the native mail client.
I must say that S/MIME support in iOS is pretty good.
Windows Phone
Even more annoying than the lack of support for browsers other than Internet Explorer is the complete absence of support for Windows Phone 10. If you install your S/MIME certificate and try to use it to sign your emails, this happens:
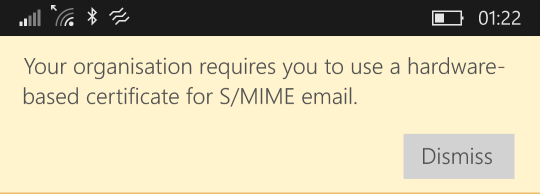
I seem to remember it working when I was on Windows Phone 8.1, but I've upgraded to Windows Phone 10 since then.
Conclusion
S/MIME is not a new technology and yet it is still relatively unsupported. If you're using a PC then you can use Outlook or Thunderbird (which is free) quite easily and, depite not having used it before, I think it's actually slightly more intuitive using Thunderbird.
If you want to use S/MIME when you're out and about then, if you're using an iPhone, it's quite a nice experience. Unless you're using Outlook of course, in which case it's not supported. Unfortunately, if you're on Windows Phone 10 you're out of luck. I seem to remember it worked with Windows Phone 8.1 but, since I have now upgraded, that doesn't help me.
Before I started writing this article, I expected to find myself preferring to use Microsoft Outlook both on my PC and also on my Windows Phone. As it is, I am torn between Thunderbird and Outlook on the desktop and, if I want to send and receive encrypted emails on the move, it looks like I might need to use my old iPhone. I hope to be able to update this article with instructions for using Windows Phone 10 in due course, but I honestly don't know if it will be possible.
Next time we'll be looking at PGP and I find myself wondering how that will pan out.
Feel free to let me know about your experiences using S/MIME (good or bad) in the comments section. If you've somehow got it to work with Windows Phone 10, please tell me how you've managed it.
Image credit: bluebay/Shutterstock.com